The Hidden Risk in E-commerce
For most e-commerce businesses, growth starts on a screen. You optimize product pages, refine your ad strategy, and look for ways to reduce friction across the customer journey. But even the most digital brand still relies on physical operations behind the scenes. Inventory has to be stored, shipments have to move, and teams, vendors, and couriers all need to access real-world spaces. When those systems work, customers barely notice. When they break down, the impact is immediate.
A missed delivery, unauthorized entry, or inventory loss creates more than a temporary disruption. It can delay fulfillment, increase support volume, and erode customer trust. For businesses operating on tight margins and high customer expectations, those problems add up quickly.
This risk grows as operations grow more complex. More locations, more vendors, more delivery volume, and more people moving through physical spaces can create vulnerabilities that are easy to overlook when most attention is focused on digital performance.
That’s why physical access control deserves a place in the broader e-commerce conversation. Protecting revenue is not only about improving conversions and acquiring customers. It’s also about securing the real-world systems that support the business behind the scenes.
Building a resilient e-commerce brand means looking beyond the screen.
Why Physical Security Matters for Dropshipping & E-commerce
Dropshipping is often seen as a low-risk, asset-light business model. Without the need to own or manage inventory directly, many operators assume physical security is someone else’s responsibility. But in reality, your business still depends on a network of physical touch points, and each one introduces risk.
Even if you never step inside a warehouse, your products do. Inventory moves through supplier facilities, third-party logistics (3PL) centers, and distribution hubs before reaching your customers. Along the way, there are multiple moments where things can go wrong: misplaced stock, unauthorized access, or breakdowns in delivery coordination.
When a package is delayed, lost, or stolen, your customer doesn’t see a supplier or logistics partner. They see your brand.
That means every gap in physical security can translate into:
– Refund requests and chargebacks
– Negative reviews and support tickets
– Lower repeat purchase rates
As order volume increases, so does the complexity. More shipments mean more handoffs. More vendors mean more people with access to physical spaces. Without clear oversight into who can enter facilities or handle inventory, it becomes harder to maintain consistency and control.
There is also the challenge of shared environments. Many e-commerce businesses rely on co-warehousing spaces or multi-tenant fulfillment centers, where multiple companies operate under one roof. In these settings, access is often distributed across staff, contractors, and delivery personnel, making it difficult to track who’s coming and going.
The result is a growing disconnect: highly optimized digital storefronts supported by physical operations that lack the same level of visibility and control.
Common Physical Vulnerabilities in E-commerce Operations
As e-commerce operations scale, physical processes often evolve organically rather than strategically. New suppliers are added, fulfillment partners change, and delivery volume increases, but the systems used to manage access and security don’t always keep up. Over time, this creates gaps that are easy to miss but costly to ignore.
Here are some of the most common physical vulnerabilities that impact e-commerce and dropshipping businesses:
1. Uncontrolled Facility Access
In many fulfillment environments, especially shared warehouses or multi-tenant spaces, access is distributed across a wide range of people, staff, third-party vendors, cleaning crews, and delivery personnel.
Without a centralized way to manage who can enter and when, access quickly becomes difficult to control. Credentials may be shared, permissions may not be updated, and former vendors may retain entry longer than intended.
When too many people can access a space without clear oversight, it becomes harder to prevent or investigate issues like inventory loss or unauthorized activity.
2. Lack of Visibility Into Activity
Knowing that something went wrong is one thing. Knowing when, where, and how it happened is another. Many e-commerce operators rely on partners or facilities that lack detailed access logs or tracking systems. This means there is little visibility into who entered a space, at what time, or for what purpose.
When issues arise, such as missing inventory, damaged goods, or delayed shipments, this lack of visibility slows down resolution and makes it harder to identify the root cause.
3. Inefficient Key and Credential Management
Traditional access methods like physical keys or keycards are difficult to manage at scale. Keys can be lost, copied, or passed between individuals without oversight. Keycards can remain active long after someone no longer needs access.
For e-commerce businesses working with multiple vendors or temporary staff, this creates unnecessary risk. Each new partner or delivery driver introduces another layer of access that must be managed manually.
4. Delivery and Entry Friction
High order volume means frequent deliveries, and each delivery requires access. In many cases, drivers arrive at facilities that are locked, unattended, or difficult to navigate.
When entry is not streamlined, deliveries can be missed, delayed, or left unsecured. This not only impacts fulfillment timelines but also increases the risk of theft or damage. For businesses that rely on speed and reliability, even small inefficiencies at the point of entry can create ripple effects across the entire customer experience.
5. Overreliance on Manual Coordination
Many access-related tasks still depend on manual processes: coordinating entry over phone calls, sharing codes via text, or relying on someone to be physically present to unlock a door.
This may work at a smaller scale, but it becomes unsustainable as operations grow. Manual coordination introduces delays, increases the chance of human error, and limits the ability to scale efficiently.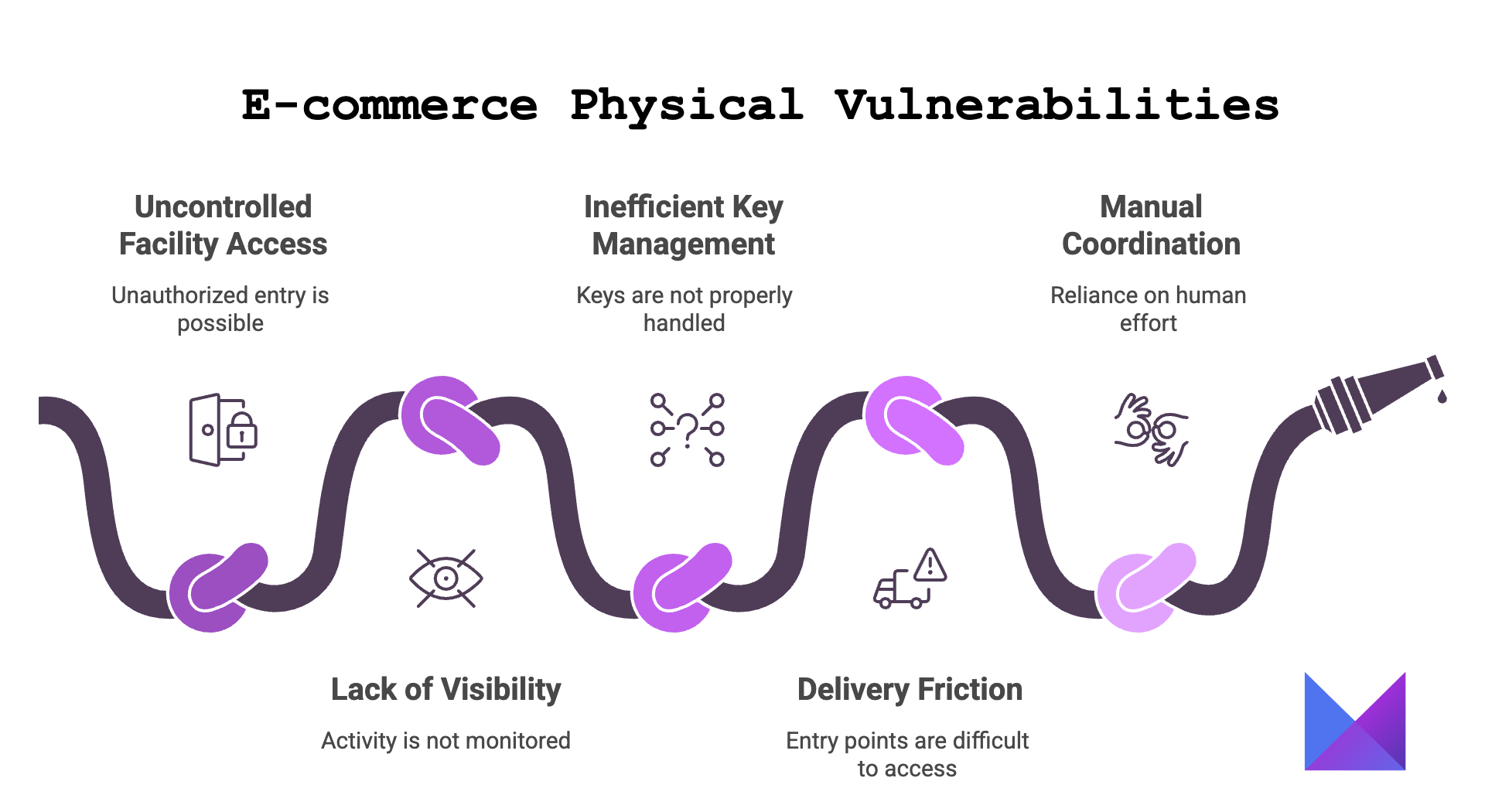
How Modern Access Control Solves These Problems
Addressing physical vulnerabilities in e-commerce operations starts with rethinking how access is managed. Traditional methods, like keys, shared codes, or manual coordination, were not designed for the speed, scale, and complexity of modern logistics, but modern access control systems are.
What is Physical Access Control?
At its core, physical access control is a way to manage and monitor who can enter a space, when they can enter, and under what conditions. While older systems rely on physical credentials like keys or fobs, newer solutions are cloud-based and designed to be managed remotely.
Instead of distributing access manually, with a tool like ButterflyMX, operators can control permissions through a centralized platform, often from a desktop or mobile device.
Key Capabilities That Address Common Gaps
Modern access control systems are built to solve the exact challenges e-commerce businesses face as they scale:
– Remote Access Management. Grant or revoke access instantly without needing to be on-site. This is especially useful when working with multiple vendors, temporary staff, or rotating delivery personnel.
– Audit Trails and Activity Logs. Track who entered a space and when. This creates accountability and makes it easier to investigate issues like missing inventory or unauthorized access.
– Reduced Reliance on Physical Credentials. By moving away from keys and shared codes, businesses can minimize the risk of lost, copied, or misused credentials.
– Centralized Oversight Across Locations. For operators managing multiple facilities or working with distributed partners, access can be controlled from a single interface rather than handled separately at each site.
From Reactive to Proactive Operations
One of the biggest advantages of modern access control is the shift from reactive problem-solving to proactive management.
Instead of responding to missed deliveries or investigating issues after they occur, businesses can put systems in place that prevent these problems from happening in the first place. Access becomes structured, trackable, and aligned with operational needs, rather than improvised.
For growing e-commerce brands, this level of control is about building a more reliable and scalable foundation for day-to-day operations.
Use Case: Securing Your E-commerce Operations End-to-End
To understand the impact of modern access control, it helps to look at how it applies across the different stages of an e-commerce operation. While each business setup is unique, most rely on a combination of storage, fulfillment, and delivery environments.
Warehouse and Storage Management
Whether you use a dedicated warehouse, a shared facility, or a smaller storage unit, controlling who can access inventory is critical.
With modern systems, you can:
– Grant access only to authorized staff
– Adjust permissions as roles change
– Maintain a record of all entry activity
Third-Party Logistics (3PL) and Vendor Access
Working with external partners introduces flexibility and complexity. Vendors, contractors, and logistics teams may need temporary or limited access to facilities.
Instead of relying on shared credentials or manual coordination, access can be:
– Issued for specific timeframes
– Restricted to certain entry points
– Revoked immediately when no longer needed
Delivery and Courier Coordination
Deliveries are one of the most frequent and vulnerable touchpoints in e-commerce operations.
Modern access control can streamline this process by:
– Allowing secure entry for couriers without requiring someone on-site
– Reducing missed or failed delivery attempts
– Minimizing the need for packages to be left unattended
Multi-Location Oversight
As businesses grow, operations often expand across multiple sites, whether through additional warehouses, new markets, or different logistics partners.
A centralized access control system allows operators to:
– Manage all locations from a single platform
– Maintain consistent security standards
– Scale operations without adding complexity
Final Thoughts: E-commerce Doesn’t Stop at the Screen
E-commerce may begin with a click, but it’s sustained by everything that happens after. Inventory is stored, orders are processed, and deliveries are completed in the physical world, whether you see it directly or not.
As operations grow, so does the need for structure behind the scenes. What starts as a flexible, lightweight setup can quickly become complex, with more vendors, more locations, and more moving parts to manage. Without the right systems in place, small inefficiencies and security gaps can scale alongside your business.
The most resilient e-commerce brands recognize that digital performance and physical operations are closely connected. A seamless customer experience depends just as much on reliable fulfillment and secure access as it does on a well-optimized storefront.
By taking a more proactive approach to how physical spaces are managed, especially when it comes to access and visibility, businesses can reduce risk, improve efficiency, and create a stronger operational foundation for growth.






